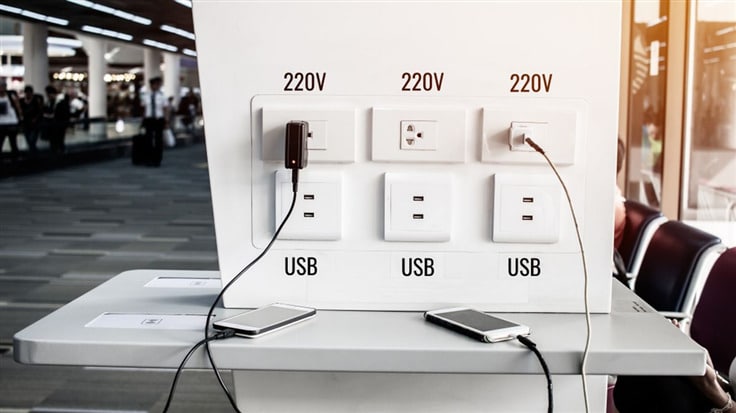
Picture this: you’re at the airport, and your phone’s battery is running low. Desperate for a quick charge, you plug your phone into a public USB port, unknowingly putting your personal data at risk.
This is juice jacking, a cyberattack that exploits the data-sharing vulnerability of public USB ports during device charging.
In this article, you’ll learn about juice jacking, how it works, its impact on mobile devices, and, most importantly, how to protect yourself.
On This Page:
Short Summary
- Juice jacking is a malicious cyberattack that can lead to data loss and unauthorized access.
- Know the different types of juice jacking attacks, recognize high-risk locations, and take preventive measures like using secure charging alternatives or USB data blockers.
- If your device has been attacked, respond quickly by removing it from the compromised port/station & running antivirus software & changing passwords.
Understanding Juice Jacking
Juice jacking is a cyberattack that exploits the vulnerability of public USB ports and cables during device charging, allowing hackers to steal personal data or install malware. It’s a real security threat, especially in high-traffic areas like airports, where people often make quick decisions without considering the potential risks.
To help you stay vigilant, we’ll dive into how juice jacking works and its impact on mobile device security.
How Does Juice Jacking Work?
Juice jacking takes advantage of the fact that USB ports and cables are designed for both charging and data transfer. When you plug your mobile device into a corrupted USB port or compromised charging station, attackers can secretly transfer data from your device or install malware without your knowledge. This can result in devastating consequences, such as identity theft, financial damage, and more.
To execute a juice jacking attack, bad actors typically tamper with public USB charging stations by installing malicious hardware or software. Once your mobile device is connected to an infected charging station, the attacker can access your data, install malware, or even take control of your device.
The best defense against juice jacking is awareness and prevention.
Avoid using free charging stations in airports, hotels or shopping centers. Bad actors have figured out ways to use public USB ports to introduce malware and monitoring software onto devices. Carry your own charger and USB cord and use an electrical outlet instead. pic.twitter.com/9T62SYen9T
— FBI Denver (@FBIDenver) April 6, 2023
The Impact on Mobile Devices
The consequences of falling victim to a juice jacking attack can be severe. Data loss, device slowdown, unauthorized access to personal information, and increased vulnerability to other malware attacks are just a few of the potential outcomes. The risks extend beyond just your device, as attackers can also gain access to your online accounts and sensitive information, such as passwords and credit card numbers.
Moreover, the risk of juice jacking is not limited to just Android devices; iOS devices can also be affected, although the risks may be lower due to stricter security measures in place for data transfers. Regardless of the type of device you own, it’s crucial to be aware of the dangers and take steps to protect yourself from juice jacking.
Common Types of Juice Jacking Attacks
There are various types of juice jacking attacks, each with its own set of risks and consequences. In this section, we’ll explore three common types: data theft attacks, malware installation attacks, and multi-device and disabling attacks.
Data Theft Attacks
Data theft attacks involve stealing personal information from devices connected to compromised USB ports, putting sensitive data at risk. When a device is connected to a public USB charging station that has been tampered with, attackers can access and export personal data, including passwords, credit card numbers, and other sensitive information.
Malware Installation Attacks
Malware installation attacks involve uploading malicious software to a device through a compromised USB port, leading to data loss, device slowdown, and other issues. Once malware is installed on a device, attackers can gain unauthorized access to the device’s data, monitor the user’s activities, and even control the device remotely.
These attacks are particularly dangerous because they can go undetected for long periods, allowing attackers to gather data and potentially cause more significant damage over time.
Multi-Device and Disabling Attacks
Multi-device and disabling attacks involve infecting multiple devices at once or disabling a connected device for the user while loading malware onto it for the attacker. In a multi-device attack, an attacker injects malware into a USB charging port, which then spreads to other devices connected to the same charging station, compromising multiple devices at once.
In a disabling attack, malicious software is loaded onto a device through a USB port, disabling it for the user and giving the attacker control.
To protect yourself from these types of attacks, always be cautious when using public charging stations and consider using secure charging alternatives like personal power banks, implement software security measures such as malware and monitoring software, and use USB data blockers.
Recognizing High-Risk Locations for Juice Jacking

High-risk locations for juice jacking are typically public USB charging stations, especially for business travelers in airports and other high-traffic areas where users may be more likely to make quick decisions without considering security risks. In these locations, people often plug their devices into free charging stations without thinking about the potential risks, making it easier for attackers to carry out juice jacking attacks.
To minimize the risk of juice jacking, be cautious when charging your electronic devices in public places and consider using secure charging alternatives or USB data blockers.
By staying vigilant and aware of the risks, you can protect your devices and personal information from juice jacking attacks.
Prevention Strategies: Safeguarding Your Device from Juice Jacking

In this section, we’ll discuss various prevention strategies to help you safeguard your device from juice jacking attacks and keep your sensitive personal information safe.
Choosing Secure Charging Alternatives
One of the best ways to protect against juice jacking is to use secure charging alternatives instead of public USB ports. Options like wall outlets, USB batteries, and charging-only cables without data transfer pins can help you charge your device without putting your personal information at risk.
Another effective prevention strategy is to use portable power banks, wireless charging stations, or portable wall chargers for your mobile phone. These devices can be charged at home and taken with you, allowing you to charge your device securely on the go.
Implementing Software Security Measures
Implementing software security measures on your device can help protect against juice jacking. Locking your phone and disabling pairing if your device is jailbroken can prevent unauthorized access to your device and personal information.
Additionally, using a VPN and disabling USB debugging can help further secure your device.
Regularly updating your device’s operating system, apps, and antivirus software can also provide additional protection against juice jacking attacks. By staying up-to-date on software updates and security measures, you can reduce the risk of falling victim to juice jacking.
Utilizing USB Data Blockers
USB data blockers, also known as USB condoms, can be an effective way to prevent juice jacking by blocking data transfer through a USB cable. These devices plug into your charging cable and sit between your device and a public USB charging station, allowing power to flow but blocking any data transfer.
By using a USB data blocker, you can charge your device at a public charging station with a USB charger without worrying about your personal information being stolen or malware being installed on your device.
USB data blockers are an affordable and portable solution to avoid juice jacking attacks.
Responding to a Juice Jacking Attack

If you’ve fallen victim to a juice jacking attack, it’s essential to take immediate action to minimize the damage. First, remove your device from the charging port and stop using the compromised charging station.
Next, take steps to remove any malware from your device, such as running antivirus software and following any necessary removal procedures.
Once you’ve addressed the malware, change any compromised passwords and monitor your accounts for suspicious activity.
By taking these steps, you can help mitigate the damage caused by a juice jacking attack and protect your personal information from further harm.
Summary
Juice jacking is a real security threat that can have severe consequences for your devices and personal information. By understanding how juice jacking works, recognizing high-risk locations, and implementing prevention strategies such as secure charging alternatives, software security measures, and USB data blockers, you can protect yourself from this dangerous cyberattack.
Stay vigilant and always consider the risks when charging your device in public spaces.
Frequently Asked Questions
How does juice jacking work?
Juice jacking is a type of cyberattack that uses malicious USB ports or charging stations to transfer malware or data without your knowledge, allowing attackers to access your device and its information.
This type of attack can be used to steal data, install malware, or even take control of your device. It is important to be aware of the risks associated with using public USB ports or charging stations, and to take steps to protect yourself.
What are the common types of juice jacking attacks?
Juice jacking attacks can come in a variety of forms, such as data theft attacks, malware installation attacks, and multi-device and disabling attacks.
How can I protect myself from juice jacking?
You can protect yourself from juice jacking by using a USB data blocker, installing security software on your connected devices, and looking for secure charging alternatives.