Cyber threats are becoming increasingly sophisticated and frequent, posing immense risks to organizations of all sizes. A robust cybersecurity incident response plan is no longer a luxury but essential for businesses to protect their critical assets. Are you prepared to handle cyber threats when they strike?
Let’s dive into creating a cybersecurity incident response plan and explore how you can make an effective strategy to safeguard your organization.
On This Page:
- Key Takeaways
- The Importance of a Cyber Incident Response Plan
- Key Components of an Effective Incident Response Plan (IRP)
- Choosing the Right Framework: NIST vs. SANS
- Training and Continuous Improvement
- Incident Response Plan Templates and Examples
- The Role of Security Orchestration, Automation, and Response (SOAR)
- Legal and Regulatory Compliance
- Summary
- Frequently Asked Questions
Key Takeaways
- Creating an incident response plan is essential for reducing the impact of cyber threats and protecting your organization’s reputation.
- It should include roles & responsibilities, communication protocols, detection/analysis procedures, containment strategies & more.
- Make sure to choose the proper framework for your needs and integrate technology solutions like SOAR tools to stay compliant with legal requirements.
The Importance of a Cyber Incident Response Plan

Imagine the potential costs and reputational damage your organization could face in the event of data breaches. Merchant processors could impose fines between $5,000 and $50,000, while card brands could charge you fees ranging from $5,000 to $500,000. A forensic investigation alone could cost anywhere from $12,000 to $100,000.
Given these high stakes, a well-crafted incident response plan is essential to mitigate the impact of cyber threats, curtail related costs, and safeguard your company’s reputation.
An effective cybersecurity incident response plan helps organizations prepare for potential cyber threats by outlining incident response plans, which include:
- Incident definitions
- Escalation requirements
- Personnel responsibilities
- Key steps to follow
- Contacts to reach out to in case of an incident
Clear incident response procedures enable your business to act swiftly and decisively during security incidents, thereby protecting sensitive data and preserving customer confidence.
Key Components of an Effective Incident Response Plan (IRP)
A successful incident response plan comprises four key incident response phases, which together form the incident response process:
- Defining roles and responsibilities
- Establishing communication protocols
- Developing procedures for detection and analysis
- Implementing containment, eradication, and recovery strategies
Addressing these essential elements allows your organization to lay a solid foundation for effective response to cyber threats and minimization of potential security incident damages, including the prevention of a security or data breach.
Remember, the preparation phase marks the first critical step towards creating a cyber incident response plan. This involves assessing your organization’s needs based on factors like size, number of employees, and how much sensitive data you store.
Once you have a clear understanding of your organization’s needs, you can then move on to the other components of the IRP to ensure a comprehensive and robust approach to incident response.
Defining Roles and Responsibilities
One of the critical aspects of an effective incident response plan is the formation of a cross-functional Cyber Incident Response Team (CIRT) consisting of incident response team members. The team should involve staff from multiple fields, such as:
- Management
- Technical
- Legal
- Communications
- Security committee liaisons
In addition to the CIRT, organizations should also consider collaborating with external incident response teams to enhance their security incident management capabilities.
Ensuring representation of all areas of expertise is necessary. Each member of the CIRT should have clearly defined roles and responsibilities, ensuring that the team can act quickly and thoroughly when dealing with an incident.
For example, the IT Security department is responsible for tracking down the source of the attack and containing it while informing other employees of the necessary actions to take. On the other hand, legal and PR professionals handle all external communication and associated processes, ensuring that the organization complies with legal and regulatory requirements.
Establishing Communication Protocols
Efficient communication is vital during a security incident. Establishing communication protocols within your incident response plan ensures that information is shared promptly and accurately within the organization, as well as with external stakeholders such as law enforcement, regulators, and affected parties.
These communication protocols should include guidelines for reporting incidents, responding to incidents, and communicating with stakeholders. Additionally, providing personnel with training on these communication protocols is imperative, so they grasp and follow them accurately during an incident.
Developing Procedures for Detection and Analysis

To effectively manage and mitigate a cybersecurity incident, your incident response plan should include procedures for:
- Early detection
- Analysis of the incident
- Prioritization of actions
- Containment and forensics
Following established frameworks like NIST or SANS allows you to ascertain the incidence, severity, and type of incident.
Developing these procedures is vital for identifying the nature and extent of a security incident, enabling your organization to act swiftly and decisively in response to potential threats. Utilizing established frameworks ensures a comprehensive and robust approach to incident detection and analysis, ultimately protecting your critical assets and sensitive data.
Implementing Containment, Eradication, and Recovery Strategies
Once an incident has been detected and analyzed, the next step is to implement containment, eradication, and recovery strategies. This involves stopping the effects of the incident, addressing the root cause, and restoring systems to their pre-compromised state.
Containment is crucial to prevent further harm and preserve forensic data, while eradication involves eliminating the cyber threat and separating any infected systems.
During the recovery phase, affected systems and devices are restored and reintroduced into the business environment. The following steps should be taken during this phase:
- Harden the systems by implementing security measures to protect against future attacks.
- Patch any vulnerabilities in the systems to ensure they are up-to-date and secure.
- Replace any compromised hardware or software to eliminate any potential threats.
- Test the restored systems to ensure they are functioning properly and are free from malware or other malicious activity.
- Monitor the restored systems for any suspicious activity to ensure no lingering malware infection or Advanced Persistent Threat (APT) remains.
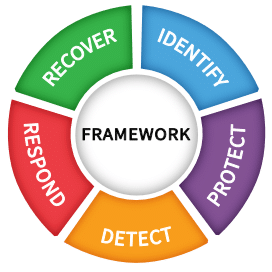
Choosing the Right Framework: NIST vs. SANS
Selecting the most suitable framework for your organization’s incident response plan is an important decision. NIST (National Institute of Standards and Technology) and SANS (SysAdmin, Audit, Network, and Security) are two highly-regarded frameworks that offer comprehensive guidance for incident response planning. While both frameworks have similarities, there are some distinctions in their approaches and focus areas.
The NIST framework provides a broader range of guidance and is more all-encompassing, whereas the SANS framework is more security-oriented and offers more in-depth guidance on triage and prioritization.
Ultimately, the choice between NIST and SANS will depend on your organization’s preferences and resources, as well as the specific needs and requirements of your incident response plan.
| Feature/Aspect | NIST | SANS |
|---|---|---|
| Origin | U.S. government agency. | Private company. |
| Focus | Comprehensive cybersecurity framework. | Specializes in training and certification. |
| Scope | Broad; covers various industries. | More focused on specific security practices. |
| Flexibility | Highly adaptable to different business needs. | More rigid, specific guidelines. |
| Implementation Cost | Variable; can be tailored to budget. | Often higher due to training costs. |
| User Friendliness | Moderate; requires some expertise. | Easier to follow due to step-by-step guides. |
| Compliance | Widely accepted for compliance. | Not as commonly used for compliance. |
| Updates | Regular, but less frequent. | More frequent updates and courses. |
| Community Support | Extensive documentation, less community interaction. | Strong community and forums. |
| Best For | Businesses needing a flexible, comprehensive approach. | Businesses looking for specific, actionable guidelines. |
| Official Website | Visit NIST | Visit SANS |
Training and Continuous Improvement

Regular training and continuous improvement are crucial for maintaining an effective and up-to-date incident response plan. This includes:
- Regularly testing and updating the IRP
- Conducting tabletop exercises
- Ensuring that your incident response team has the appropriate certifications and educational opportunities.
Investing in training and continuous improvement allows your organization to:
- Identify and address any weaknesses or gaps in the incident response plan
- Ensure the plan remains up-to-date and effective against evolving cyber threats
- Reinforce essential security information and practices among employees
- Reduce the likelihood of human error during an actual incident
This ensures that your incident response plan is robust and effective in protecting your organization against cyber threats.
Incident Response Plan Templates and Examples
Creating a customized incident response plan for your organization can seem daunting, but fortunately, there are numerous templates and examples available to help guide you through the process. Some valuable resources for templates and examples include:
These resources offer valuable templates and examples for various industries and organizational needs.
These templates and examples can assist you in tailoring a plan that meets your organization’s specific requirements, ensuring that your incident response plan effectively addresses the unique risks and challenges your business faces.
Leveraging these resources helps establish a solid foundation for your incident response plan, enhancing your organization’s protection against potential cyber threats.
The Role of Security Orchestration, Automation, and Response (SOAR)
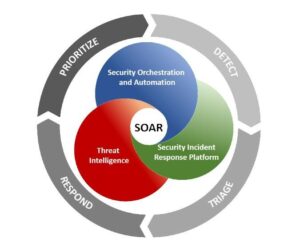
Incorporating technology solutions like Security Orchestration, Automation, and Response (SOAR) tools into your incident response plan can greatly enhance its effectiveness and efficiency. SOAR tools automate incident response processes, making them faster and more reliable, as well as reducing the chances of human error.
Integrating SOAR tools and other technology solutions like incident response software, network security monitoring tools, and risk-based alerting solutions enhances your organization’s ability to detect, analyze, and respond to cyber threats.
This ultimately results in a more comprehensive and robust incident response plan that can better protect your organization from potential cybersecurity incidents.
Legal and Regulatory Compliance
Legal and regulatory compliance is a critical aspect of incident response planning, as breach notification laws require organizations to have an incident response plan in place. Compliance of your plan with all relevant laws, regulations, and client obligations is vital to avoid potential fines and penalties during a security incident.
In addition to meeting legal and regulatory requirements, your incident response plan should also address any specific requirements imposed by industry-specific regulatory and certification bodies.
Collaborating with a cyber lawyer to review and refine your plan can help ensure that it remains compliant with all applicable rules and obligations, further protecting your organization from potential legal and regulatory risks.
Summary
A comprehensive and robust cybersecurity incident response plan is essential for organizations to effectively manage and mitigate the risks associated with cyber threats. By addressing key components such as defining roles and responsibilities, establishing communication protocols, developing procedures for detection and analysis, and implementing containment, eradication, and recovery strategies, you can build a solid foundation for protecting your organization’s critical assets and sensitive data.
Regular training, continuous improvement, and adherence to legal and regulatory requirements further enhance the effectiveness of your incident response plan, ensuring that your organization is well-equipped to handle cyber threats when they strike.
Frequently Asked Questions
How do you write an incident response plan?
To write an incident response plan, determine employee roles and security policies, understand what needs to happen during a crisis, train the staff, form an incident response team and define responsibilities, develop playbooks, create a communication plan, test the plan, identify lessons learned, and keep testing and updating the plan.
What is included in a cyber incident response plan?
A cyber incident response plan includes guidelines for roles and responsibilities, communication plans, and standardized response protocols to prepare for, identify, respond to, and recover from a cyber attack.
What are the differences between the NIST and SANS incident response frameworks?
The NIST framework provides a broader scope of guidance when responding to an incident, while the SANS framework focuses more on security-related tasks such as triage and prioritization.
How can SOAR tools enhance incident response planning?
SOAR tools can streamline and optimize incident response planning, making processes faster and more reliable while reducing the chances of human error.